Published on Thu Sep 11 2025 19:00:00 GMT-0500 (Central Daylight Time) by Orkid Labs
It’s Friday. The inbox is full, investors are texting, and the demo needs to be both dazzling and safe. This week was about protecting users and our IP while keeping velocity high — a story about purpose-built constraints, not just features.
Why demo-only matters (and why “just pause it” wasn’t enough)
We needed to prove — on-chain and off — that the system is in a read-only state for investor demos. The easy pitch is to “pause” contracts. The real world reply: legacy contracts weren’t pausable and weren’t upgradeable proxies. So we did what disciplined teams do: we created ABI-preserving guarded contracts that revert all writes with “demo-only,” and we re-point the app to those addresses. Investors can verify this directly on-chain.
Highlights:
- ABI preserved; state-changing calls revert with “demo-only”
- Reads are safe (zeroed or guarded)
- New addresses published and linked in the docs
CI/CD: when org migrations break your deploys
We moved registries (repo migration), and the deploys silently pulled from the wrong Docker image paths. CI was pushing to the right org; the server was still pulling from the old one. Fixes:
- Updated workflows to tag/pull from the new org registry paths
- Taught the deploy workflow to handle manual triggers cleanly and to fall back to
latestif a SHA tag isn’t present - Added an org-level token fallback for GHCR pulls
- Health checks plus guarded rollback logic
Lesson: org moves break the invisible glue first. Automate the boring parts; make fallbacks explicit.
WebSockets, auth, and demo-friendly UX
A demo that requires an API key to even connect isn’t a demo — so we:
- Allowed anonymous WS connections when
DISABLE_AUTH=true - Ensured the frontend connects to the correct backend domain in prod (no stray subdomains)
- Always create the WS worker; don’t require an apiKey just to show data in demo mode
The on-chain path we took
- Confirmed legacy contracts were not proxies (no “Read/Write as Proxy” tabs)
- Wrote a lockdown script for best-effort Pausable/AccessControl cases, plus source deactivation hooks
- Deployed two new contracts on Polygon mainnet:
- GuardedArbitrageExecutor: 0xB4a4355a62dbbB8E67DaC455C321890Eea22654a
- Tx: 0x84d1b374dcf4d5c1e3deca17cda63865659f536ed026c4d74cf9c9a173cf2cbd
- GuardedEventStreamReconciler: 0xbAE395a77dad3D0e34127F7ae270042cb33cD632
- Tx: 0xee9c5d17748e41d2b102b76da2d663938e0bcc687a02c649899befd4a1a1870e
- GuardedArbitrageExecutor: 0xB4a4355a62dbbB8E67DaC455C321890Eea22654a
- Verified behavior:
- executeTwoHopArb → reverts “demo-only”
- getReconciledPrices → zeroed or guarded
Tooling choices (and why)
Hardhat v3 is ESM-only, and we didn’t want to flip the repo’s module type for a quick ship. We added a tiny, isolated subpackage for deployment, and a solc-based fallback deployer to bypass local Hardhat bootstrap quirks. Principle: keep the blast radius small; ship the outcome.
Principles we leaned on
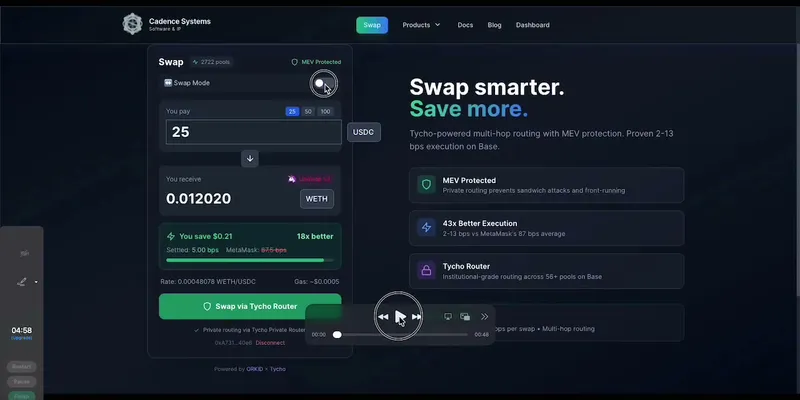
- Private by default for MEV-sensitive flows (simulate → private → controlled fallback)
- One provider/client per network; reuse connections; backoff + jitter
- Rate limit and cache hot reads; batch, don’t N+1
- Observability beats ceremony: structured logs; health checks; measurable rollbacks
- Demo mode must be obvious to users and provable to auditors (on-chain + app guards)
What we shipped (user-facing)
- Demo-only enforcement (backend + frontend flags)
- ABI-preserving guarded contracts deployed on Polygon
- Updated docs with addresses and verification steps
- Deploy pipeline that works after an org migration
- Anonymous WebSocket demo capability
Lessons learned (for founders and teams)
- “Just flip the switch” isn’t a strategy — it’s a hope. Design the off-ramp on day one.
- Your riskiest failure modes hide in wiring: registries, tokens, and envs — not glamorous, but existential.
- If your demo is slow to set up or finicky about keys, you’ll miss the moment. Remove drag.
- Be generous with your safety rails. You’ll never regret a guard that prevented a bad day.
What’s next
- Surface more telemetry on chain conditions and route selection (without leaking details)
- Expand demo-only analytics with clear disclaimers (simulate ≠ guarantee)
- Continue the TypeScript porting plan for the physics engine integration
If you’re evaluating MEV products, ask for realism: real gas, realistic execution constraints, and the courage to disable trading in a demo without losing insight. That’s what we’re building.
Editor’s note: This post was updated on September 19, 2025 to include a custom Open Graph image for improved social media sharing. No content changes were made.
Written by Orkid Labs
← Back to blog